MFT CYBERSECURITY STRATEGY
SECURE-BY-DESIGN
REGULARLY TESTED AGAINST KNOWN SECURITY VULNERABILITIES
BUILT-IN, EASY-TO-USE PGP ENCRYPTION
Let us know your data transfer requirements and we’ll be in touch
An Encrypted MFT Software Solution that sits perfectly within your Cybersecurity Strategy
Managed File Transfer (MFT) software is a critical tool for businesses of all sizes that need to securely transfer files. MFT software provides features such as encryption, auditing, and logging to help businesses to protect their data from unauthorized access and cyberattacks.
MFT found itself in the spotlight in 2023 following a series of high-profile cyberattacks targeting well-known vendors and affecting thousands of customers and millions of users. The Cl0p ransomware attacks affecting MOVEit MFT software were a significant reminder of the importance of cybersecurity.
Because of these events, we expect to see enterprises taking stock of their managed file transfer processes and investing in secure-by-design solutions. That means growth in the adoption of MFT software, driven by several factors, including:
- The increasing need to share data with external partners and customers.
- The growing threat of cyberattacks, including ransomware.
- The increasing complexity of IT systems and applications.
- The need to comply with data protection regulations (HIPAA / HITECH, etc.).
- Trading partners mandating stronger encryption methods (i.e., PGP and SFTP).
DIPLOMAT MFT SECURITY FEATURES:
 Diplomat MFT is a secure-by-design managed file transfer (MFT) software solution. This means that security is considered at every stage of the development process, from initial design to final implementation.
Diplomat MFT is a secure-by-design managed file transfer (MFT) software solution. This means that security is considered at every stage of the development process, from initial design to final implementation.
Some of the key security features of Diplomat MFT include:
- Encryption: Diplomat MFT encrypts all data at rest and in transit using industry-standard encryption algorithms, including PGP and SFTP.
- Authentication: Diplomat MFT supports a variety of authentication mechanisms, including multi-factor authentication, to ensure that only authorized users can access the system.
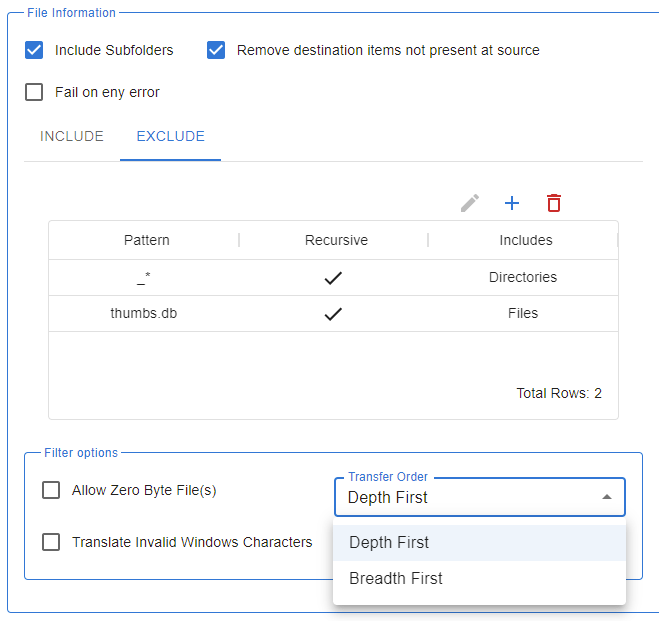
- Authorization: Diplomat MFT uses granular permissions to control who can access and manipulate files and folders.
- Auditing: Diplomat MFT logs all activity for auditing and compliance purposes.
In addition to these security features, Diplomat MFT is a robust MFT software solution scalable to meet the needs of businesses of all sizes and can be deployed on-premises, in the cloud, or in a hybrid environment.
DIPLOMAT MFT IS SECURE-BY-DESIGN:
Here are some specific examples of how Diplomat MFT is secure-by-design:
- The Diplomat MFT codebase is regularly reviewed by security experts to identify and fix any potential vulnerabilities.
- Diplomat MFT uses a variety of security best practices, such as input validation and output encoding, to prevent common security attacks.
- Diplomat MFT is regularly tested against known security vulnerabilities.
- Diplomat MFT uses process automation to minimize the potential for human error.
- Diplomat MFT supports file encryption with PGP and encrypted transport with SFTP.
- Diplomat MFT’s Edge Gateway prevents exposure of files and data to the public internet.
Diplomat MFT is a secure and robust MFT software solution that helps businesses protect their data from unauthorized access, modification, or destruction. modification, or destruction.
Cybersecurity MFT
Frequently Asked Questions
I use a different MFT product. Am I vulnerable to this zero-day exploit?
Each software vendor creates their own software in their own way. A vulnerability in one solution does not mean that it exists in all solutions. For example, when the Log4j vulnerability was disclosed, it was severe as the utility was widely used in many—but not all—software products. Our Diplomat MFT family of managed file transfer platforms, for example, was unaffected because we don’t use Log4j, while other software might.
If there are any questions about whether this exploit affects the security of the managed file transfer product you use, you should contact your vendor immediately.
Is Coviant Software’s Diplomat MFT platform safe from this zero-day exploit?
Yes. The vulnerability present in the product in question does not exist with Diplomat MFT. The weakness at issue was related to an option for accessing an administration console in the cloud, and due to bug(s) in the code that implemented an administrative function specific to that product. Because Diplomat MFT is different software that does not have this vulnerable code path, it is not susceptible to this zero-day exploit.
I use a different MFT product. Could a similar vulnerability put my MFT software at risk?
Most software products are complex, and every software product is likely to have some bugs. Some bugs may affect performance, while others may affect security. One strategy software developers use to mitigate the risk of bugs causing severe problems is to lock down code execution paths, making them available only for appropriate access. For example, if you have internet-accessible endpoints, they mabe susceptible to exploitation if a bug exists. To minimize risk, developers may choose to limit access only to authenticated users with an affirmed need. For example, restricting administration and monitoring functions to the corporate network, not the Internet.
My organization uses a solution that was developed in-house. Are we safe?
When information security and data privacy are involved, organizations should only purchase software from reputable vendors who employ good security practices when they develop software. That includes full documentation of every update, conducting regular testing, patching, and security audits, and providing excellent technical and customer support.
I was looking at different MFT options and now I’m concerned about security. What should I do?
Don’t abandon the search. Secure managed file transfer software is still a vital part of any comprehensive data security program. MFT software that automatically encrypts files, uses secure communications protocols, documents processes for auditability, and confirms transfer success and alerts of any trouble is important for sharing vital files throughout the digital supply chain. Financial data, medical data, intellectual property, and other sensitive information that your organization needs to protect should only be shared using a secure managed file transfer platform.
Isn't SFTP and MFT the same?
There is sometimes a misconception that SFTP and MFT are the same thing, however, this could not be further from the truth. Secure File Transfer Protocol (SFTP) is a file protocol for transferring large files over the web by using secure shell encryption to provide a high level of security. Managed File Transfer encompasses a lot more than just being a file transfer protocol. Managed file transfer (MFT) software is a technology platform that enables the secure, reliable, and automated transfer of data between organizations, systems and people. Data reliability, integrity, cyber security and compliance are key fundamentals aspects of any managed file transfer solution.
What can I do to ensure my managed file transfer is secure?
Conduct informed due diligence before making an investment in a managed file transfer product. Then, maintaining proper configuration is very important. Understand the software and its security architecture and policies. Do not expose the administration portal to the internet; instead, restrict access to the admin functions of the software to only those secure, back-end networks and/or machines that need access. Use a VPN or Bastion Host to access those administrative tools from remote locations. Ensure your administrative interface is only accessible behind your firewall via your back-end network, and that it is available only to those endpoints that should have access. Use edge gateways into the internet-facing DMZ. Never forsake security in favor of convenience.
What is the difference between Diplomat MFT and other managed file transfer products?
We believe in keeping things simple. After twenty years of providing an excellent managed file transfer platform we’ve learned some things, and that experience means we engineer our award-winning Diplomat MFT to do the task of transfering files simply, securely, and reliably. There are no unnecessary features or endless options–software bloat–increasing product complexity and the risk of failure. A managed file transfer platform should be easy to use, robust, and prioritize cybersecurity.
Using this experience to inform your evaluation of secure MFT products can help you to make a better decision. Of course, we’d be honored if our award-winning Diplomat MFT software were included in your search. We are confident that Diplomat MFT is engineered to be secure and perform as needed at whatever scale or volume you require. And our passion for customer and technical support is tops in the industry.
What is a Cybersecurity Strategy?
A cybersecurity strategy tends to be a high-level plan for how an organization will secure and protect its data infrastructure and assets, usually for a 3 to 5 year period. An effective cybersecurity will require good data awareness, data management, company communication along with frequent updates and checks.
Here are some of the key components of a cybersecurity strategy:
- Risk assessment: Identify and assess the organization’s cybersecurity risks. This includes identifying the organization’s assets, vulnerabilities, and threats.
- Security controls: Implement security controls to mitigate identified risks. This may include physical security controls, technical security controls, and administrative security controls.
- Incident response: Develop an incident response plan to deal with cybersecurity incidents. This plan should include procedures for identifying, containing, eradicating, and recovering from cyberattacks.
- Cybersecurity awareness and training: Educate and train employees on cybersecurity risks and best practices. This helps to reduce the risk of human error, which is a major factor in cyberattacks.
- Monitoring and maintenance: Regularly monitor and maintain security systems to ensure that they are effective in protecting the organization’s assets.
Businesses that utilize managed file transfer (MFT) should consider the following additional cybersecurity considerations:
- Secure file transfer protocols: Use secure file transfer protocols, such as FTPS, SFTP, and AS2, to protect data in transit.
- Encryption: Encrypt data both at rest and in transit to protect it from unauthorized access.
- Access control: Implement strong access controls to restrict access to sensitive data.
- Logging and auditing: Log and audit all file transfers to track activity and identify potential security breaches.
- Vulnerability management: Regularly scan for and remediate vulnerabilities in MFT software.
- Incident response: Incorporate MFT into the organization’s incident response plan.
By implementing these cybersecurity considerations, businesses that utilize MFT can help to protect their sensitive data from unauthorized access, modification, or destruction.
How does MFT Software support a Cybersecurity Strategy?
MFT is something we experience in our every day lives with it powering important functions such as healthcare file transfer, global money market exchanges through to order processing and tracking. MFT software alleviates the complexity of file and data transfers by automatically meeting the security, compliance and performance requirements which are necessary to send and receive important business files and sensitive data.
One important way MFT promotes a strong cybersecurity defence is that MFT uses various methods of encryption (i.e PGP encryptiuon) to secure both the contents of a message, called data layer encryption, and the means of transporting that message, called transport layer encryption.
MFT systems are playing an ever-larger role in organizations, replacing legacy file transfer systems and ad hoc tools with a unified, streamlined approach that eliminates waste and duplication.
What are the Data Security Risks of FTP Custom Scripts?
In the past it has been commonplace for IT departments to adopt a DIY approach to file transfer processes and we can’t blame them. Particularly for a business function that may have been overlooked, under resourced and poorly understood. Early days these may have started with manual processes then evolved to legacy FTP scripted solutions.
Any good future-proofed cybersecurity plan would look to identify these custom scripts as posing a possible risk to the data infrastructure and have a plan to remove or at least reduce the reliance on these scripted solutions. Homegrown scripted solutions are trying to handle an ever increasing number of files transfers and contend with a number of complex integrations.
In addition to a loss of productivity, this can invite a range of issues including a lack of control, data security, compliance and visibility. Ultimately, these will impact on a businesses time, resources and costs.
Can MFT be used to protect Data Security in the Cloud?
The benefits of the cloud have enticed many organizations to adopt, or at least consider, some sort of cloud environment. Gartner forecasts that cloud-deployed organizations will experience fewer security incidents in upcoming years, and in general, cloud-stored data is often considered more secure than data kept on company-run servers.
Managed file transfer (MFT) solutions provide businesses with helpful features such as automation, custom workflows, security settings, audit trails and reports. These features allow businesses to scale up their data exchange requirements and operations, which is especially beneficial when moving to a cloud environment.
It’s important to remember within a cybersecurity strategy that Cloud security is a two-way street. Researching each cloud provider’s cybersecurity methods and selecting the best one for your organization is a vital step toward ensuring your data’s integrity. But it’s not the only step. IT teams are just as responsible for the security of their sensitive business data as the cloud platforms that hold it.
How can Managed File Transfer Software support your Cybersecurity Strategy?
For an average company, 80% of data exists as files and 30% of business critical processes involve file transfers. The demand on technology to craft business solutions is ever growing, which we’ve seen with the rise of remote working. However, this can allow for greater risks to businesses such as data theft and loss, data breaches and vulnerability to sophisticated malware attacks. Now is the time to ensure your cybersecurity strategy and software tools are able to protect your data infrastructure as best as possible.
Preventing Data Breaches with MFT Cloud Software
There has been some notable data breach horror stories, for example, the 2017 RNC data breach. The data firm they used placed an unencrypted database containing the information of 198 million American voters on an equally unsecured AWS server. If the firm had routinely monitored the cloud for vulnerabilities, the breach could’ve been prevented.
Cybersecurity Trends 2024 and beyond:
The technological landscape is constantly evolving, and 2024 will be no exception. Some of the key trends that we can expect to see in the coming year include:
CL0P RANSOMWARE:

The Cl0p ransomware attack on MoveIT in 2023 was a high-profile example of the dangers of ransomware attacks. Cl0p ransomware is a type of malware that encrypts a victim’s files and demands a ransom payment in exchange for the decryption key.
In 2024, we expect to see continued activity from Cl0p and other ransomware gangs. Businesses need to be prepared for the possibility of a ransomware attack by implementing strong security measures, such as backing up their data regularly and using secure MFT software to safely transfer files.
The Cl0p ransomware attacks affecting MOVEit MFT software were a significant reminder of the importance of cybersecurity. Organizations that use MFT solutions should take steps to mitigate the risk of attack by:
- Keeping their software up to date. Software vendors regularly release updates to patch security vulnerabilities. It is important to install these updates as soon as they are available.
- Segmenting their networks. Segmenting a network into different zones can help to contain the spread of malware in the event of a breach.
- Implementing strong authentication. Strong authentication measures, such as multi-factor authentication, can help to prevent unauthorized access to systems and data.
- Educating their employees about cybersecurity best practices. Employees should be trained to identify and avoid phishing emails and other social engineering attacks.
Looking for an alternative to MOVEit MFT? CLICK HERE >>
Please do not hesitate to contact us to speak to one of our MFT experts. We will be more than happy to demo Diplomat MFT or set you up with a free trial.
Cybersecurity & Cyber Resilience:
Cybersecurity is a top priority for businesses of all sizes, driving an expected increase in cybersecurity investments, including those using artificial intelligence (AI) and machine learning (ML) AI and ML-based security solutions can help businesses to detect and respond to cyberattacks more quickly and effectively. These solutions can also help businesses to identify and mitigate security risks before they are exploited by attackers.
What is cyber resilience?
Cyber resilience is the ability of an organization to quickly detect, prevent, respond to, and recover from cyberattacks. It is a holistic approach to cybersecurity that encompasses people, processes, and technology. Cyber resilience is important because cyberattacks are becoming more frequent and sophisticated.
Organizations of all sizes and in all industries are at risk of being targeted. A cyberattack can have a devastating impact on an organization, leading to financial losses, reputational damage, and even operational disruption.
TIPS FOR CYBER RESILIENCE IN 2024 AND BEYOND
Here are some tips for building cyber resilience in 2024 and beyond:
- Adopt a zero-trust security model. A zero-trust security model assumes that no user or device can be trusted by default. This means that all users and devices must be verified before they are granted access to resources.
- Implement security automation and orchestration. Security automation and orchestration (SAO) tools can help organizations to automate repetitive security tasks and to orchestrate the response to security incidents.
- Invest in user education and training. Employees are often the weakest link in the security chain. It is important to provide employees with regular security awareness training and to educate them about the latest cyber threats.
- Develop a cyber incident response plan. A cyber incident response plan (CIRP) is a blueprint for how an organization will respond to a cyberattack. A CIRP should include steps for identifying, containing, eradicating, and recovering from a cyberattack.
- Test your security posture regularly. It is important to regularly test your security posture to identify and mitigate vulnerabilities. This can be done through penetration testing, attack simulations, vulnerability scanning, and risk assessments.
CYBER RESILIENCE > FUTURE TRENDS
Here are some future trends in cyber resilience:
- Increased use of artificial intelligence and machine learning (AI/ML). AI/ML can be used to improve the detection and prevention of cyberattacks. AI/ML can also be used to automate security tasks and to orchestrate the response to security incidents.
- Growing importance of supply chain security. Organizations are increasingly dependent on their suppliers. A cyberattack on a supplier can have a cascading effect on its customers. Organizations need to work with their suppliers to improve their security posture.
- Increased focus on resilience against ransomware attacks. Ransomware attacks are becoming more common and more disruptive. Organizations need to implement strong security measures to protect themselves from ransomware attacks and to develop a plan for recovering from a ransomware attack if one does occur.
Cyber resilience is essential for organizations of all sizes and in all industries. By following the tips above, organizations can improve their cyber resilience and protect themselves from the latest cyber threats.
SFTP SERVERS:
SFTP servers are a secure way to transfer files over the internet. SFTP servers use SSH encryption to protect files from unauthorized access and interception.
In 2024, we can expect to see increased adoption of SFTP servers as businesses look for secure ways to transfer files. SFTP servers are a good option for businesses of all sizes, but they are especially well-suited for businesses that need to transfer sensitive data.
An SFTP server provides assurances that an organization’s file exchanges with external parties will be handled securely across any network by using the strongest cryptography available to prevent interception or manipulation by malicious actors via man-in-the-middle attacks.
Coviant Software offers an SFTP server option as a part of the Diplomat MFT family of products. Our SFTP server provides out-of-the-box no-code file transfer process automation, PGP encryption, compression operations, enterprise-grade scalability to support organizations of any size with secure file transfers of any volume, and web-based administration with an easy to navigate user interface.
When combined with our Coviant Software Edge Gateway, the SFTP Server brokers SFTP traffic from your DMZ to the back-end network without requiring any inbound holes in your back-end firewall. This ensures that no data remains in the DMZ, and all authentication and access control is securely managed by your back-end systems. This defense-in-depth approach significantly increases your company’s security posture.

CASE STUDIES

READ THE FULL CASE STUDY
CUSTOMER:
CHRISTUS HEALTH
COVIANT PRODUCT:
DIPLOMAT MFT ENTERPRISE EDITION

READ THE FULL CASE STUDY
CUSTOMER:
CONRAIL
COVIANT PRODUCT:
DIPLOMAT MFT STANDARD EDITION

READ THE FULL CASE STUDY
CUSTOMER:
MOLINA HEALTHCARE
COVIANT PRODUCT:
DIPLOMAT MFT ENTERPRISE EDITION
AUTOMATION
Out of the Box Automation capabilities
SFTP & PGP Encryption
Security enabled through SFTP and PGP encryption.
EDGE GATEWAY
Protect your SFTP Server with our Edge Gateway
DIPLOMAT MFT v9.2
We continue to invest and improve Diplomat MFT.