 If you want to have the best chance of accomplishing something worthwhile, you’ve got to have a plan. Trusting to luck doesn’t qualify. Instead, you have to set a goal, assess your current situation, and map out the steps needed to progress to your objective. That includes identifying vital resources, quantifying success, and periodically evaluating where you are and making whatever adjustments are needed to stay on track. It’s helpful when you can learn from the experience of others who have done what you want to do.
If you want to have the best chance of accomplishing something worthwhile, you’ve got to have a plan. Trusting to luck doesn’t qualify. Instead, you have to set a goal, assess your current situation, and map out the steps needed to progress to your objective. That includes identifying vital resources, quantifying success, and periodically evaluating where you are and making whatever adjustments are needed to stay on track. It’s helpful when you can learn from the experience of others who have done what you want to do.
For organizations struggling to keep their systems and data secure against the ever-present threat of a data breach, having a plan to improve your security posture and minimize operational risks is key. Every organization collects, stores, and moves information in the course of doing business, and so guarding against cyberattacks and preventing errors that compromise data are imperative. And these things don’t happen by accident; they take thoughtful planning, faithful execution, and regular evaluation. Fortunately, there are a number of frameworks available for organizations that need a proven model for creating their own cybersecurity strategies.
Plenty to Choose From
Where cybersecurity is concerned, there is no single plan that can work for every organization. Different industries have to be concerned with different threats and regulatory regimes, but there are frameworks that can be used to identify the biggest risks and considerations. From there more specific elements can be added. Recently, the cybersecurity site HelpNet Security ran an article entitled “10 cybersecurity frameworks you need to know about” to help organizations looking for a place to get started. We suggest reading the full article for more information about each, but here are the ten frameworks they identified:
- CIS Critical Security Controls
- Control Objectives for Information and Related Technologies (COBIT)
- CSA Cloud Controls Matrix (CCM)
- HITRUST Cybersecurity Framework (CSF)
- ISO/IEC 27001:2022
- Katakri
- NIST Cybersecurity Framework (CSF)
- Payment Card Industry Data Security Standard (PCI DSS)
- Secure Controls Framework (SCF)
- Standard of Good Practice for Information Security (SOGP)
That list is far from exhaustive, but it is an excellent place to start. Most organizations will find one or two frameworks that they can use to create their own cybersecurity plan. And depending on your industry there are often trade groups that can provide further guidance specific to your needs. But what happens once you’ve launched your organization’s cybersecurity strategy?
Measure and Improve
 The National Institute of Standards and Technology (NIST) offers a guide for setting quantifiable goals, measuring performance, and improving your organization’s plan no matter what framework it adopts. Announced last week on the NIST website, the NIST Special Publication (SP) 800-55 Revision 2: Measurement Guide for Information Security, is “intended to help organizations move from general statements about risk level toward a more coherent picture founded on hard data.” NIST is soliciting public comments on the guide through March 18, 2024.
The National Institute of Standards and Technology (NIST) offers a guide for setting quantifiable goals, measuring performance, and improving your organization’s plan no matter what framework it adopts. Announced last week on the NIST website, the NIST Special Publication (SP) 800-55 Revision 2: Measurement Guide for Information Security, is “intended to help organizations move from general statements about risk level toward a more coherent picture founded on hard data.” NIST is soliciting public comments on the guide through March 18, 2024.
The NIST Measurement Guide states that, “Information security measurement enables organizations to quantify improvements or gaps in securing systems and demonstrate quantifiable progress in accomplishing strategic goals and objectives.” Looking through the current draft, the NIST Measurement Guide emphasizes the importance of measuring performance and results, and will help security leaders and practitioners alike to better evaluate their own programs and advocate for resources in ways that are quantifiable.
 I Love It When a Plan Comes Together
I Love It When a Plan Comes Together
Hannibal Smith once said, “I love it when a plan comes together.” If he had been a CISO instead of the leader of the A Team, you can bet he would have operated with a cybersecurity strategy based on one of the available frameworks. And he’d probably make sure his plan was coming together by using the NIST Measurement Guide to track its progress.
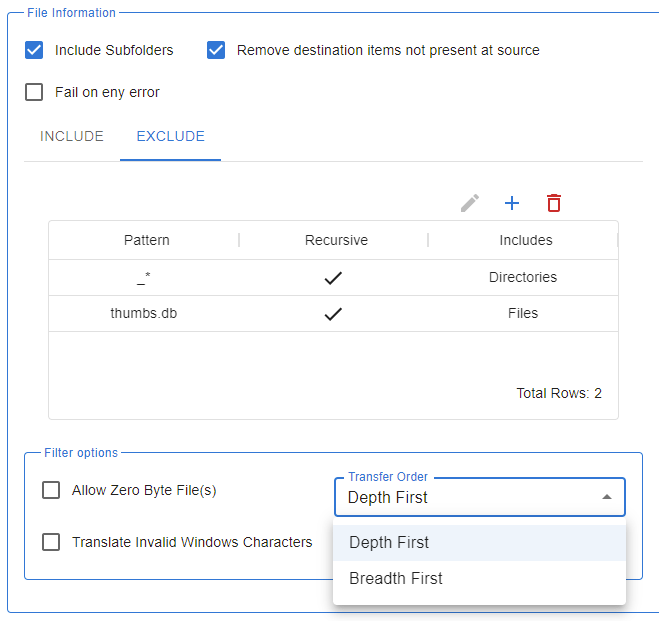
If your cybersecurity plans require a secure managed file transfer solution (and why wouldn’t they?) get in touch.